
Load Balancer settings when migrating from Exchange 2010 to Exchange Server 2016
Exchange Server 2016 supports coexistence with Exchange Server 2010 Update Rollup 11 and later. Planning and configuring load balancer settings is critical for Exchange Server configuration, and it plays a crucial role when coexistence and migration projects are in progress. Since many organization are looking to update from their older Exchange Server 2010 deployments to Exchange Server 2016, this article helps you to understand the considerations to address for coexistence configurations.
Configuring the Load Balancer when Migrating from Exchange 2010 to Exchange 2016
Upgrading or migrating between versions of Exchange Server required careful planning to deliver a seamless user experience with no downtime. When organizations are migrating from Exchange 2010 to Exchange 2013, it may take some time to complete the project. As a result, it is essential to configure the previous and new Exchange systems to coexist. A correctly configured load balancer setup can make this possible.
Users can access Exchange Server email in many ways including Outlook clients on multiple devices, Outlook on the Web, Active Sync, and others. There are various protocols that clients use to connect to the Exchange Server, and these can all be configured to use the load balancers in place. The protocols are:
- Outlook Web App (OWA)
- Autodiscover
- Exchange Web services (EWS)
- Exchange Active Sync(EAS)
- Offline Address book (OAB)
- Outlook Anywhere
- MAPI
- SMTP Protocol
The table below shows the Exchange 2010 Internal and External URL configuration that will be used on the Exchange 2010 CAS Servers.
| Virtual Directory | Internal URL | External URL |
|---|---|---|
| OWA Virtual Directory | https://mail.domain.com/OWA | https://mail.domain.com/OWA |
| ECP Virtual Directory | https://mail.domain.com/ECP | https://mail.domain.com/ECP |
| OAB Virtual Directory | https://mail.domain.com/OAB | https://mail.domain.com/OAB |
| WebService Virtual Directory | https://mail.domain.com/EWS/Exchange.asmx | https://mail.domain.com/EWS/Exchange.asmx |
| ActiveSync Virtual Directory | https://mail.domain.com/Microsoft-Server-ActiveSync | https://mail.domain.com/Microsoft-Server-ActiveSync |
| AutoDiscoverServer Internal URI | https://autodiscover.domain.com | https://autodiscover.domain.com/MAPI |
| CAS Array | Outlook.domain.com | |
| Outlook Anywhere | http://mail.domain.com |
Figure 1 shows a typical Exchange 2010 deployment with a load balancer, and how different client connection types are handled.
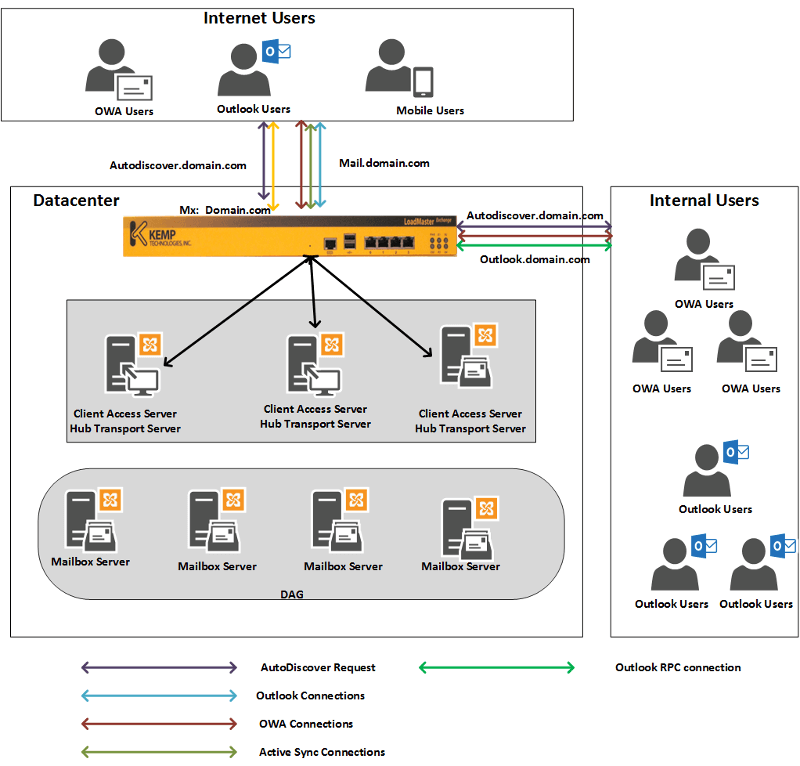
Figure 1. Current Exchange 2010 organizations before introduction Exchange 2016
Exchange Organizations after introducing Exchange 2016
As servers running Exchange 2016 Server are introduced into an organization the same CAS URLs and name space from Exchange 2010 can be used, with one addition for Outlook Anywhere as discussed below. The Table below includes the additional Outlook Anywhere URL.
| Virtual Directory | Internal URL | External URL |
|---|---|---|
| OWA Virtual Directory | https://mail.domain.com/OWA | https://mail.domain.com/OWA |
| ECP Virtual Directory | https://mail.domain.com/ECP | https://mail.domain.com/ECP |
| OAB Virtual Directory | https://mail.domain.com/OAB | https://mail.domain.com/OAB |
| WebService Virtual Directory | https://mail.domain.com/EWS/Exchange.asmx | https://mail.domain.com/EWS/Exchange.asmx |
| ActiveSync Virtual Directory | https://mail.domain.com/Microsoft-Server-ActiveSync | https://mail.domain.com/Microsoft-Server-ActiveSync |
| MAPI Virtual Directory | https://mail.domain.com/MAPI | https://mail.domain.com/MAPI |
| AutoDiscoverServer Internal URI | https://autodiscover.domain.com | https://autodiscover.domain.com/MAPI |
| Outlook Anywhere | http://mail.domain.com | |
There are two options available to allow coexistence between Exchange Server 2010 and Exchange Server 2016. They are:
- Reconfigure the Exchange Server 2010 organization, or
- Retain the existing Exchange 2010 organization.
Let’s discuss each of these options and load balancer design and role is implemented in both.
Reconfigure the Exchange Server 2010 organization
This is the recommended option from the two available. Reconfiguring the Exchange Server 2010 organization enables Outlook Anywhere for all the Exchange Server 2010 users. This makes it much easier to coexist with Exchange Server 2016 servers. All the Outlook clients should be using Outlook Anywhere as the default connection protocol. The PowerShell script below can be used to enable Outlook Anywhere on Exchange 2010 Server:
Get-ExchangeServer | Where {($_.AdminDisplayVersion -Like “Version 14*”) -And ($_.ServerRole -Like “*ClientAccess*”)} | Get-ClientAccessServer | Where {$_.OutlookAnywhereEnabled -Eq $False} | Enable-OutlookAnywhere -ClientAuthenticationMethod Basic -SSLOffloading $False -ExternalHostName mail.domain.com -IISAuthenticationMethods NTLM, Basic
Internally outlook clients does not use the Outlook Anywhere protocol by default to connect to Exchange Server, as the Outlook client by default uses the RPC protocol on high-speed networks. However, to force all the Outlook clients to use Outlook Anywhere on internal network use the PowerShell commands below on the Exchange Server. Once executed Autodiscover configures all the Outlook clients to use RPC/HTTP and uses mail.domain.com for the internal connection.
Set-OutlookProvider EXPR -OutlookProviderFlags:ServerExclusiveConnect
Set-OutlookProvider EXCH -OutlookProviderFlags:ServerExclusiveConnect
Figure 2 shows the configuration for Exchange Server 2016 and Exchange Server 2010 co-existence. With all the above Exchange Server configuration in place the load balancers need configured to work with Exchange 2016 Server to use the Mail.domain.com and Autodiscover.domain.com URLs shown in the table. This allows the clients to connect and if the target mailbox is on an Exchange 2016 Server it directly connects to the user’s mailbox. If the target mailbox is on a legacy Exchange 2010 Server then the Exchange 2016 CAS server proxies the connection to the Exchange 2010 CAS server, and this sets up the connection to the mailbox. The proxying of this connection is entirely transparent to the users.
DNS changes will also be required on the load balancer that is handling requests to the CAS servers. This is necessary to ensure that the correct requests are sent to the right Exchange 2016 and Exchange 2010 servers during the coexistence. The same will be true for load balancers directing SMTP requests if in use. The DNS changes required will be unique to each Exchange organization.
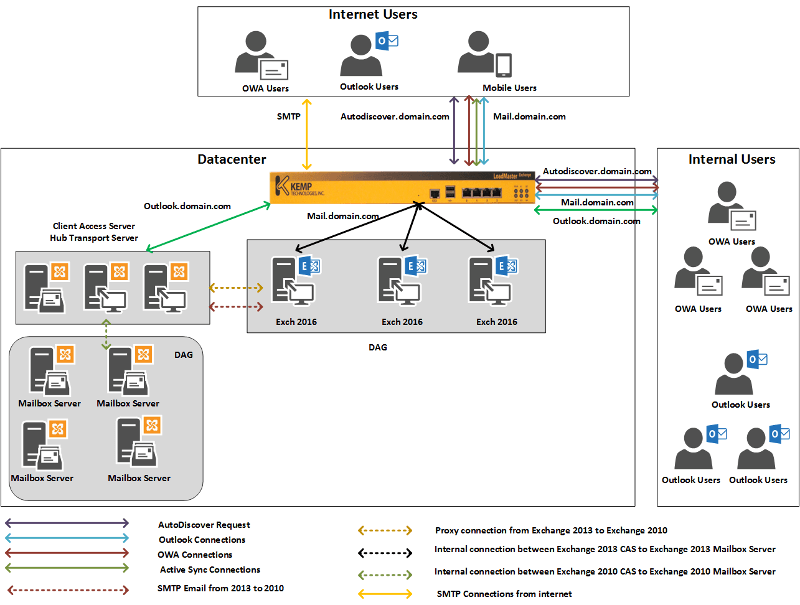
Figure 2. Exchange organizations after introduction of Exchange Server 2016
The points below outline how various protocols are proxied from Exchange 2016 to Exchange 2010:
OWA Protocol
OWA Client -> Exchange 2016 -> Proxies Connection -> Exchange 2010 CAS -> Exchange 2010 mailbox
Active Sync Protocol
Active Sync Client -> Exchange 2016 CAS -> Proxies Connection -> Exchange 2010 CAS -> Exchange 2010 mailbox
Exchange Web Service
Active Sync Client -> Exchange 2016 CAS -> Proxies Connection -> Exchange 2010 CAS -> Exchange 2010 mailbox
Outlook Anywhere
Active Sync Client -> Exchange 2016 CAS -> Proxies Connection -> Exchange 2010 CAS -> Exchange 2010 mailbox
No change the existing Exchange 2010 organization
If you decide to go for option 2 and retain the existing Exchange Server 2010 organization without modification then a few things need configured. In this scenario, Exchange 2010 Outlook Anywhere is configured with mail.domain.com and RPC traffic is set up with Outlook.comain.com. This design does not need any changes to coexist with Exchange 2016. Users could continue to use outlook.domain.com for all the RPC connections. Since the load balancer is already routing outlook.domain.com to Exchange Server 2010 no changes are required there either. However, Exchange Server 2010 users continue to use outlook.domain.com, and all Exchange 2016 users use mail.domain.com for all connections.
Configure the load balancer with the URL’s mail.domain.com and Autodiscover.domain.com to route requests and traffic to Exchange 2016 Servers. Figure 3 shows this configuration.
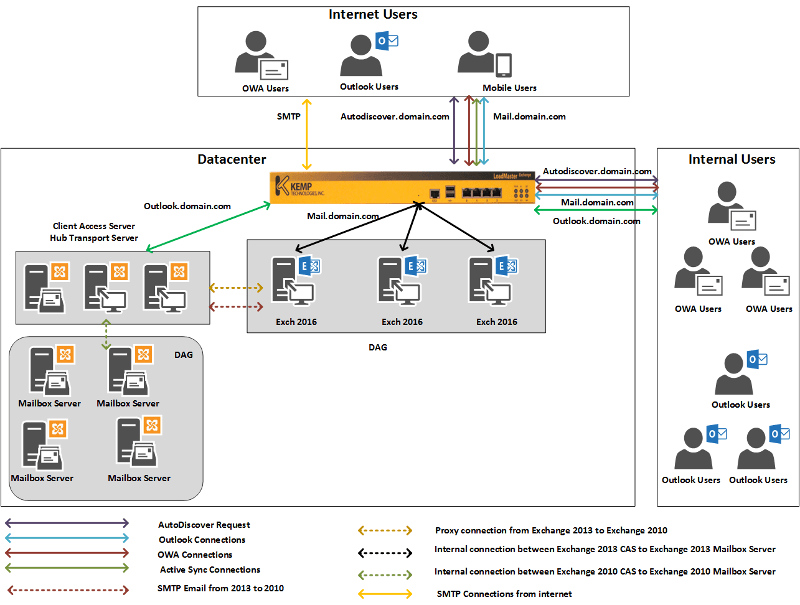
Figure 3. Mail flow with a retained Exchange Server 2010 organization.
The points below outline how various protocols are proxied from Exchange 2016 to Exchange 2010 without the organizational changes outlined for option 1:
OWA Protocol
OWA Client -> Exchange 2016 -> Proxies Connection -> Exchange 2010 CAS -> Exchange 2010 mailbox
Active Sync Protocol
Active Sync Client -> Exchange 2016 -> Proxies Connection -> Exchange 2010 CAS -> Exchange 2010 mailbox
Exchange Web Service
Active Sync Client -> Exchange 2016 -> Proxies Connection -> Exchange 2010 CAS -> Exchange 2010 mailbox
Hopefully this article series will help you to understand how a load balancer plays a role in configuring coexistence between Exchange 2010, 2013, and 2016. The next article will cover coexistence when migrating from Exchange Server 2013 to Exchange Server 2016.